Tech
Cyberwarfare Against Critical Infrastructure
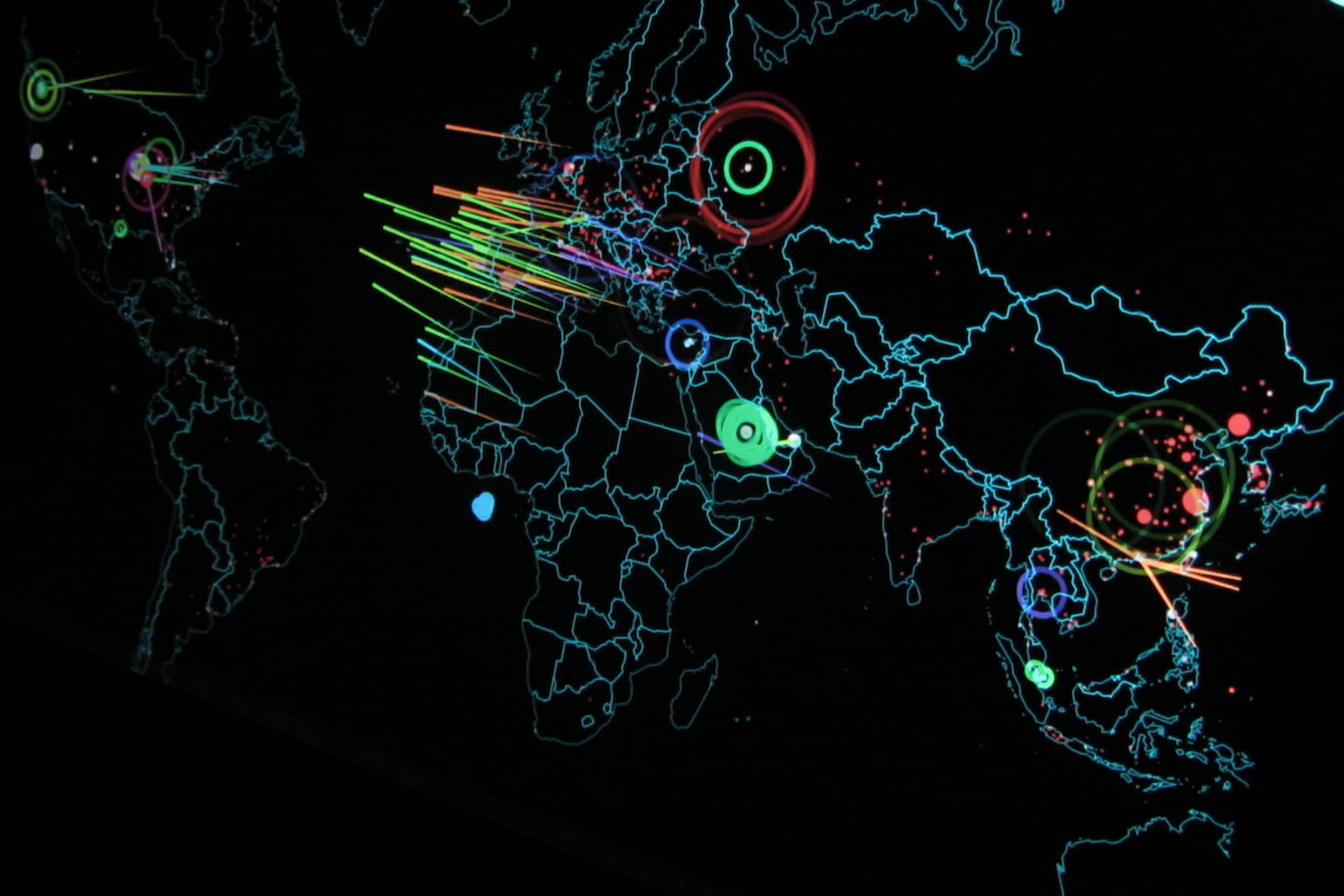
Despite the fact that cyberattacks are occurring with greater frequency and intensity around the world, many either go unreported or are under-reported, leaving the public with a false sense of security about the threat they pose and the lives and property they impact. While governments, businesses and individuals are all being targeted on an exponential basis, infrastructure has become a target of choice among both individual and state-sponsored cyber-attackers, who are targeting security systems that were previously thought of as impenetrable. This has served to demonstrate just how vulnerable cities, states and countries have become, and the growing importance of achieving global risk agility in the face of such threats.
The US government has now blamed Russia for numerous cyberattacks on its energy, aviation, and other sectors in recent years – evidence of just how significantly cyber warfare has come to define the manner in which some governments threaten and spar with each other. The Russian government planted malware, conducted spear phishing, and gained remote access to some very sensitive areas of America’s infrastructure networks. They did this with surprising ease, for example, using false job applicant resumes to apply for jobs through the companies’ human resources divisions. Once the tainted emails were opened, the malware was installed.
This modus operandi is not new to Russia, nor to other actors in cyberspace intent on planting malware and gaining entry into otherwise sensitive companies and sectors. Russia planted the malware that led to the Wannacry ransomware attacks of 2017 by entering a Ukrainian tax and accounting firm that services 80% of Ukraine’s businesses, then gaining access to all of those businesses. That quickly spun out of control and infected computers around the world. It is shockingly easy for nefarious actors to enter otherwise secure computer systems and companies. Up to 95% of the time that is because of the risk that exists between a keyboard and the chair – employees who click on an infected link.
Cyberattacks are difficult to prevent, given the relative ease with which hackers can find a single system vulnerability, and the impossibility of plugging every conceivable security hole. Cybersecurity professionals are in essence playing an endless game of cat and mouse, whereby a would-be attacker attempts to enter a system while security professionals attempt to defend a computer system from attack by applying continuous patches. The adversary then quickly moves
to exploit the latest discovered vulnerability. That is why many computer security programs produce patches numerous times per day.
High profile cyberattacks are increasingly becoming the norm, giving nations of all sizes, degrees of wealth and resources a seat at the table with China, Russia and the US, affording them a disproportionate ability to create disruption and chaos. While the big three lead the world in overt and covert cyberattacks, virtually every government with the capability to do so engages in such attacks. Iran and North Korea are prominent members of the club. All this has prompted the Trump administration to declare earlier this year that it is equating cyberattacks against critical infrastructure on a par with acts of war that can potentially result in a nuclear weapon response. The stakes are extremely high.
International treaties intended to address the problem have limited impact because of the inability to hold signatories accountable and the difficulty associated with accurately determining the identity of responsible actors. Enhanced information sharing, combined with a mandate to swiftly and accurately release information regarding attacks to impacted citizens, provide a sensible foundation for designing a protocol to effectively address future attacks, yet very few governments routinely engage in this practice.
Clearly, governments, businesses and individuals must devote greater resources to becoming more cyber-vigilant. Apart from raising awareness, devoting more resources and making counter-cyberattacks compulsory, nations must also create a more holistic approach to addressing the problem by thinking more proactively about how to address these vulnerabilities, implementing routine cybersecurity audits, and creating teams of people devoted solely to solving the problem. Budgets need to be adjusted to devote even more resources to addressing the growing list of cyberrisks to infrastructure. Security and privacy risk-mapping, benchmarking and scenario planning should become a standard part of cyberrisk management protocols.
Governments and businesses should engage in more public-private partnerships in order to adequately address the issue. President Obama issued the first Executive Order of its kind designed to establish a voluntary risk-based cybersecurity framework between the private and public sectors. The framework allowed for all US government agencies, regardless of their size or cybersecurity capability, to apply the best possible risk management practices in an effort to improve the security of critical infrastructure. The primary importance of this framework is that it allows for all those who voluntarily participate to adequately communicate and understand the risks, which is a vital step in the direction of achieving a functioning national and international cybersecurity network.
The European Union implemented the Network and Information Security Directive, which forced member states to adopt more rigid cybersecurity standards and created an avenue for EU member states and the operators of essential services such as energy, transportation, and healthcare sectors to effectively communicate. While other nations are in the process of acting accordingly, no nation allocates sufficient resources to adequately respond to the increasing threat of a cyberattacks against critical infrastructure, nor does any nation have a truly comprehensive plan to prevent or meaningfully react to the outcome of such attacks. Local and state governments must work together with their national counterparts to produce and quickly implement plans to address future attacks, because they are coming.